Digitpol, A cybersecurity and investigation firm based in The Netherlands has warned business owners to ensure Wi-Fi routers are locked down, secured, fully updated with the new security standard WPA3 implemented. Digitpol’s digital forensic researchers recently detailed new types of Wi-Fi attacks which were discovered by investigating large data leaks, all of which occurred on the WPA2 security standard. The attacks allowed hackers to crack Wi-Fi passwords on business grade routers regardless of how strong the passwords were set to. In every case, Digitpol discovered that rogue Wi-Fi devices were nearby to conduct interception.
Digitpol developed a probe named “Wi-Fi Signal Analysis” to detect Wi-Fi snooping, payload injection, rogue devices and Wi-Fi Spying in seconds, the probe operates on-location and the data is sent to an AI based database for analysis which then alerts CSO and CIO’s. The probe has prevented thousands of hacking attempts on business networks and prevented spying on devices installed.

Digitpol’s Signal Analysis Probe
Wi-Fi attacks are more common on business networks than personal ones and have been discovered in major investigations. According to cybersecurity firm Avast, a vulnerability in MikroTik WiFi routers has affected nearly 2.5 lakh routers across the globe, leaving them vulnerable to crypto-mining and other forms of cyber-attacks. Of the total affected routers, 11,809 routers in India have been affected.
Brazil is most affected with 85,230 routers being affected. Avast stated that hackers have exploited a vulnerability ‘CVE-2018-14847’. This is a vulnerability on Winbox, which is the operating system for MicroTik routers. All its versions will 6.42 allows remote attackers to bypass authentication and read arbitrary files. This then allows them to execute attacks ranging from cryptomining to eavesdropping. Avast suspects that the routers were targeted by cryptomining campaign ‘JS:InfectedMikroTik’.
According to researchers at Netlab 360, a new botnet is actively spreading its network using unpatched Wi-Fi routers such as D-Link, Huawei, Netgear, called as Mozi, it’s using telnet to exploit systems with weak passwords and adds every device into its network with a final goal of performing DDoS attack.
This botnet is first surfaced by Netlab 360’s team of threat monitoring. They’ve flagged this new botnet after studying it for nearly four months. Named as Mozi, this new botnet is found using a part of Gafgyt’s code and is based on DHT protocol.
While Gafgyt is just another malware infecting systems, Distributed Hash Table is a custom protocol based on standard ones and is used commonly in torrent clients (and other P2P services. This protocol helps in hiding its malware payload behind the huge amount of DHT traffic, thus making it harder to detect the malicious code passing through the network. Further, it’s faster to expand connections in the network without the use of servers.
After scanning the environment, Mozi finds a vulnerable device like router or CCTV with a weak password and cracks using telnet. After logging in, it then drops/executes the payload to take full control of the unpatched device. And this will be added to the P2P network immediately, once this happens hackers have full access.
Digitpol’s Wi-Fi experts are certain Wi-Fi and IOT over-the-air attacks will rise in 2020, Digitpol’s team are conducting Wi-Fi audits for business across Europe, the probe audits details such as the number of connected devices on a network, Wi-Fi traffic, approved Wi-Fi devices, security flaws, un-authorized devices and instant upgrades. The audits have so far discovered out-of-date firmware allowing remote control, hijacked routers, modified firmware, many connected un-authorised devices and active interception. The probe can be deployed as a fixed install to sites to detect Wi-Fi interference within 900ms.
Hidden Wi-Fi networks are a big issue inside commercial organisations and government, recently Digitpol identified over 18 hidden networks at one location using its Signal Analysis Probe. Wi-Fi base stations can hide or cloak their identities, these base stations are identified in the probe.
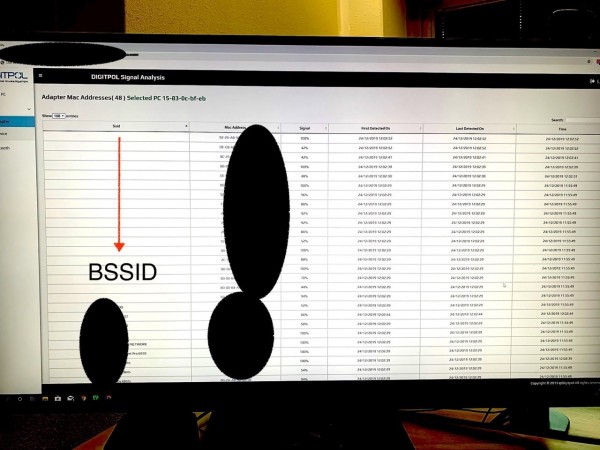
Analysis from the Signal Analysis Probe in a cloud database displays the vast number of hidden devices at a location.
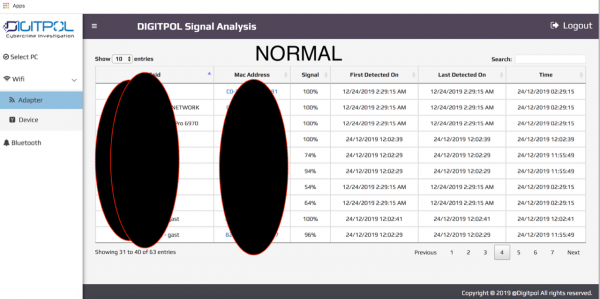
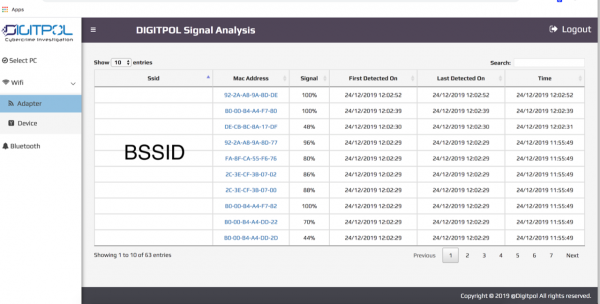
How Wi-Fi networks should look and appear with a SSID and a recognized MAC, as a comparison between hidden, abnormal and normal, the difference is clear.
Digitpol can conduct an RF site survey at your location and provide a report detailing any issues which can be traced and solved on the spot. More information is available at https://digitpol.com/wifi-network-forensics/
Media Contact
Company Name: Digitpol
Contact Person: Media Manager
Email: Send Email
Phone: +31558448040
Country: HongKong
Website: https://digitpol.com